Sublime Security
Sublime Security is an email security platform that provides detection and response for phishing and email threats using signals, automation, and security workflows.
Use Cases the Adapter Solves
- User and Asset Enrichment: Cross-reference user data from Sublime Security with device and user assets in Axonius to correlate email security incidents with organizational assets and improve threat response.
- Security Governance: Maintain an up-to-date inventory of Sublime Security user roles and permissions aligned with Axonius, enabling better access management and compliance auditing.
Asset Types Fetched
- Users
Data Retrieved through the Adapter
Users - Fields such as User ID (user_remote_id), Username, First Name, Last Name, Email Address
Before You Begin
Required Ports
- TCP port 443 (HTTPS)
Authentication Methods
Bearer Token (API Key) Authentication .
APIs
Axonius uses the Sublime Security API v0. The following endpoints are called:
GET /v0/scim/Users- List SCIM users with pagination support
Required Permissions
The following permissions are required:
API Key with Admin, Engineer, or Analyst Role (Recommended)
Supported From Version
Supported from Axonius version 8.0.22
Connecting the Adapter in Axonius
Navigate to the Adapters page, search for Sublime Security, and click on the adapter tile.
Click Add Connection.
To connect the adapter in Axonius, provide the following parameters:
Required Parameters
- Host Name or IP Address - Base URL of the Sublime Security API. Find it under Automate > API in your Sublime Security dashboard. Example:
https://api.platform.sublimesecurity.comorhttps://platform.sublime.security - API Key - API Key (Bearer Token) for authentication. This is the API key you generated in Sublime Security.
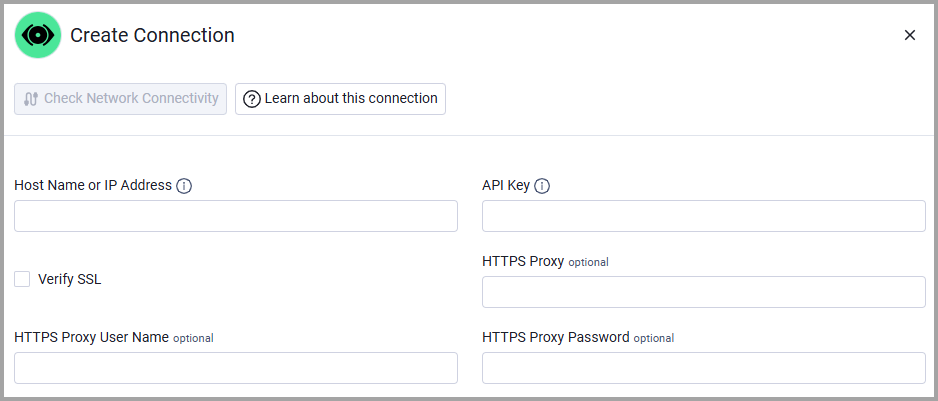
Optional Parameters
- Verify SSL - Select whether to verify the SSL certificate of the server against the CA database inside of Axonius. For more details, see SSL Trust & CA Settings.
- HTTPS Proxy - Connect the adapter to a proxy instead of directly connecting it to the domain.
- HTTPS Proxy User Name - The user name to use when connecting to the value supplied in Host Name or IP Address via the value supplied in HTTPS Proxy.
- HTTPS Proxy Password - The password to use when connecting to the server using the HTTPS Proxy.
To learn more about common adapter connection parameters and buttons, see Adding a New Adapter Connection.
.
Updated about 2 months ago
