Tenable.sc (SecurityCenter)
Tenable.sc (formerly SecurityCenter) consolidates and evaluates vulnerability data, prioritizing security risks. Note that the Source field shown in the Axonius Installed Software table for Tenable shows either Direct or Agent Scanning.
- Direct - the information about this source is updated to the Axonius fetch time from Tenable.
- Agent Scanning - the information is updated only according to the information fetched by the Tenable Agent, and up to date according to the time that the Tenable agent ran.
Asset Types Fetched
- Devices, Aggregated Security Findings, Software, SaaS Applications, Alerts/Incidents
Before You Begin
Authentication Methods
Connect the adapter with either of the following parameter pairs:
- User Name and Password
- Access Key and Secret Key
- Session Token and Session Cookie
Note
The preferred credentials to use for authentication are Access Key and Secret Key.
Required Permissions
The Tenable.sc account used to connect the adapter must have the Security Manager role, with access to all the required repositories. For details about Tenable SC user roles, see User Roles.
Connecting the Adapter in Axonius
Required Parameters
- Tenable.sc domain - The URL of the Tenable.sc management server. (e.g.,
https://tenable-sc.company.com). - User Name and Password - The credentials for a user account that has the Required Permissions to fetch assets.
OR
- Access Key and Secret Key - The API key-secret pair associated to a user account that has the Required Permissions to fetch assets.
OR
- Session Token and Session Cookie - A session cookie associated with the supplied username.
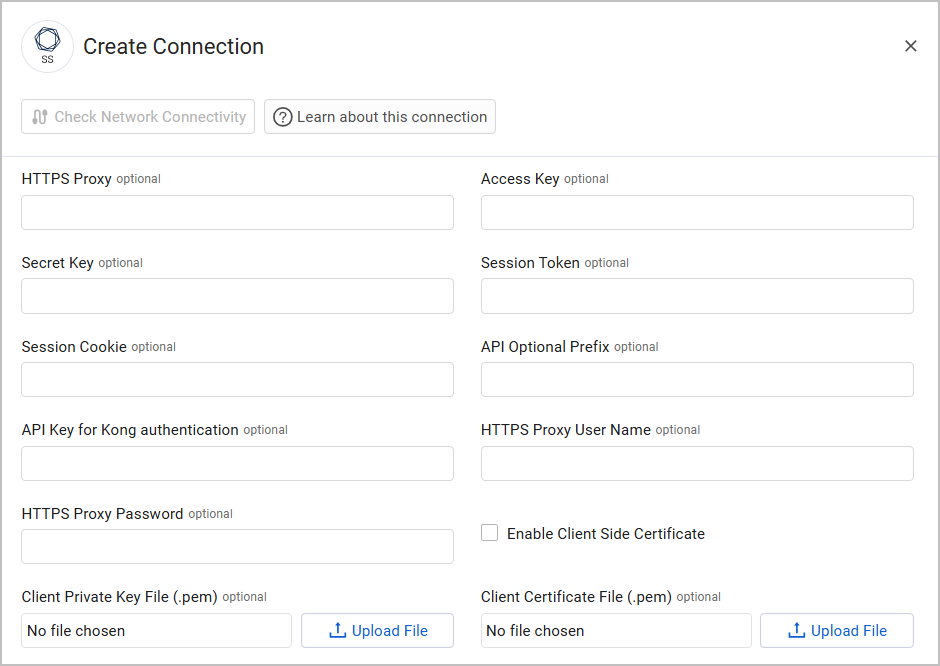
Optional Parameters
- API Optional Prefix - Optional API prefix.
- API Key for Kong authentication - The API key for authentication using the Kong API Gateway.
- Verify SSL - Select whether to verify the SSL certificate of the server against the CA database inside of Axonius. For more details, see SSL Trust & CA Settings.
- HTTPS Proxy - Connect the adapter to a proxy instead of directly connecting it to the domain.
- HTTPS Proxy User Name - The user name to use when connecting to the URL of the Tenable.sc management server via the value supplied in HTTPS Proxy.
- HTTPS Proxy Password - The password to use when connecting to the URL of the Tenable.sc management server via the value supplied in HTTPS Proxy.
- Enable Client Side Certificate - Check this option to enable Axonius to send requests using the certificates uploaded to allow Mutual TLS configuration for this adapter.
- Click Upload File next to Client Private Key File to upload a client private key file in PEM format.
- Click Upload File next to Client Certificate File to upload a public key file in PEM format.
To learn more about common adapter connection parameters and buttons, see Adding a New Adapter Connection.
Advanced Settings
Refer to Tenable.sc (SecurityCenter) Advanced Settings for the full list.
Related Enforcement Actions
Updated about 2 months ago
