Kubernetes
Kubernetes (K8s) is an open-source system for automating deployment, scaling, and management of containerized applications.
Asset Types Fetched
- Devices, Containers, Compute Images
Before You Begin
APIs
Axonius uses the Kubernetes API Server.
Required Ports
- The default port is 6443.
Required Permissions
The value supplied for the Token parameter:
- Must have read authorization to Pods and Nodes.
- Must be associated to a service account that has the following permissions:
-
Read authorizations in the APIServer. If you're using RBAC (Role Based Access Control), please refer to the official docs at https://kubernetes.io/docs/reference/access-authn-authz/rbac/.
To perform an authorization test, run the following command in your K8s cluster. If the command outputs no, it means the user doesn't have the necessary permissions.kubectl auth can-i get pods --all-namespaces --as -
Get and List permissions for namespaces. Configure the following:
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
- name: axonius-reader
- rules:
- apiGroups:
- ''
- resources:
- pods
- nodes
- namespaces
verbs:
- get
- list
-
Troubleshooting
- Make sure the cluster has ApiServer component enabled
- To perform an authentication test you can run the following command (in your K8s cluster):
curl :/api/v1/pods -H "Authorization: Bearer "- Explore the API with token: https://kubernetes.io/docs/tasks/administer-cluster/access-cluster-api/
Deploying the Adapter in Axonius
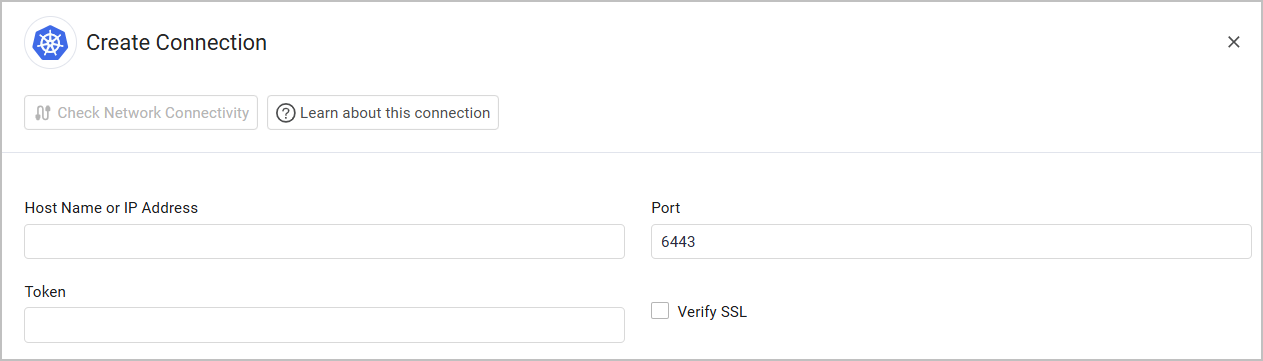
Click Add Connection and provide the following parameters:
- Host Name or IP Address - The hostname or IP address of the Kubernetes API Server endpoint that Axonius can communicate with via the Required Ports. In order to locate the IP Address of an API Server run the following command (in your K8s cluster):
kubectl config view | grep server - Port (default: 6443) - The port used in the connection.
- Token A bearer token associated with a service account that has the Required Permissions to fetch assets. For more information, see Accessing Clusters.
- To retrieve the token, first run the following command in your K8s cluster to get the list of secrets:
kubectl get secrets- Then, run this command on the relevant secret name and copy from the output the content of the token field.
kubectl describe secret - Verify SSL - Select whether to verify the SSL certificate of the server against the CA database inside of Axonius. For more details, see SSL Trust & CA Settings.
To learn more about common adapter connection parameters and buttons, see Adding a New Adapter Connection.
Advanced Settings
Note
Advanced settings can either apply to all connections for this adapter, or to a specific connection. Refer to Advanced Configuration for Adapters.
- Enrich containers with Ingress Rules - Select to enrich Container assets with Ingress rules.
Note
To learn more about Adapter Configuration tab advanced settings, see Adapter Advanced Settings.
Updated about 2 months ago
