Binary Defense MDR
Binary Defense MDR is a managed detection and response service that provides continuous monitoring, threat detection, and incident response using integrated threat intelligence and expert analysis across IT environments.
Use Cases the Adapter Solves
- Detect Unmanaged Endpoints: Identify devices monitored by Binary Defense MDR that may not be tracked in other asset management systems, ensuring complete visibility across your security infrastructure.
- Verify Security Coverage: Confirm that all critical assets are actively monitored by Binary Defense MDR and receiving threat detection and response services.
Asset Types Fetched
- Devices
Data Retrieved through the Adapter
The following data can be fetched by the adapter:
Devices - Fields such as Hostname, FQDN, Asset ID, Operating System
Before You Begin
Required Ports
- TCP port 443 (HTTPS)
Authentication Methods
API Key Authentication
APIs
Axonius uses the Binary Defense MDR API. The following endpoints are called:
GET /api/v1/assets- Retrieves asset information from Binary Defense MDR
Required Permissions
The API key must have read access to asset data.
Note: The exact permission names should be confirmed with your Binary Defense administrator or Binary Defense support, as the API documentation is not publicly available.
Supported From Version
Supported from Axonius version 8.0.21
Connecting the Adapter in Axonius
Navigate to the Adapters page, search for Binary Defense MDR, and click on the adapter tile.
Click Add Connection.
To connect the adapter in Axonius, provide the following parameters:
Required Parameters
- Host Name or IP Address - The Base URL of the Binary Defense MDR API. For example:
https://api.binarydefense.com - API Key - The API Key sent via the BD-Vision-Auth header.
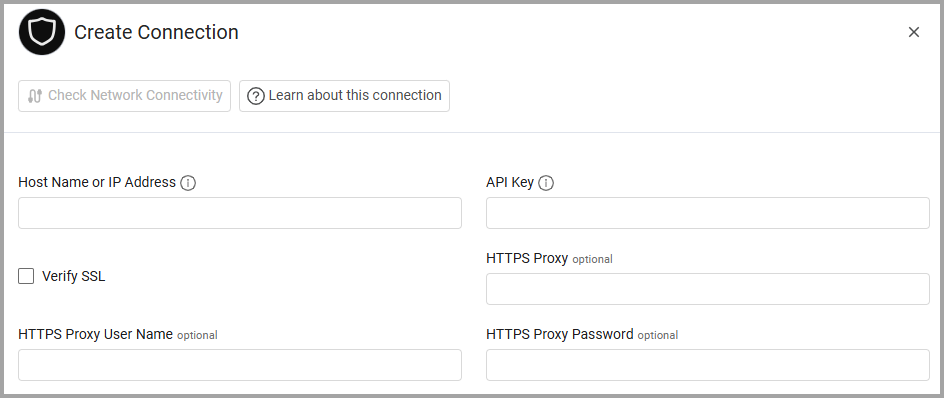
Optional Parameters
- Verify SSL - Select whether to verify the SSL certificate of the server against the CA database inside of Axonius. For more details, see SSL Trust & CA Settings.
- HTTPS Proxy - Connect the adapter to a proxy instead of directly connecting it to the domain.
- HTTPS Proxy User Name - The user name to use when connecting to the value supplied in Host Name or IP Address via the value supplied in HTTPS Proxy.
- HTTPS Proxy Password - The password to use when connecting to the server using the HTTPS Proxy.
To learn more about common adapter connection parameters and buttons, see Adding a New Adapter Connection.
Updated 20 days ago
